"Many websites are just one password away from being hacked and exploited."
That sounds like a very overdramatic statement but, in many cases, it's very much true.
Here at Adaptive, we aim not to unnecessarily alarm people or use scare tactics to sell our services. However, this particular statement really made us stop and think about not only our own website security but that of our clients and every other website out there too.
The Drupal CMS has a fantastic security record - certainly amongst the best of its peers - but any website is only as secure as you make and maintain it to be.
Over 80% of security breaches are due to weak or stolen passwords.(i)
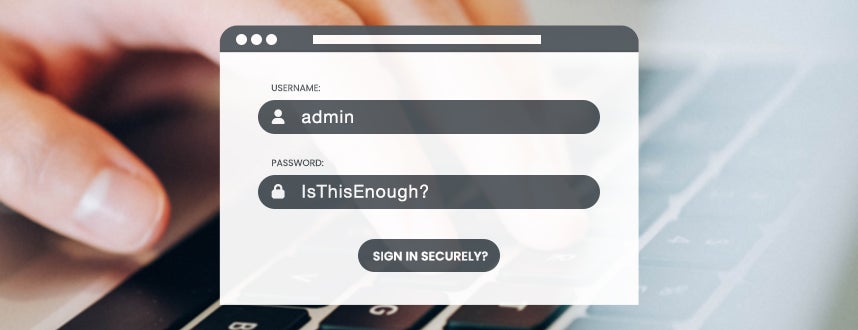
Your team's admin and editor users all log into the admin area of your website with a combination of username or email address and password - but is that really enough? Consider this...
Like the majority of CMS platforms, there are numerous clues within the visible code of your Drupal web pages that will indicate what CMS your website utilises.
Again like other platforms, logging into the admin area of your website is typically done via a URL common to the majority of installations - in Drupal's case by adding /user to the end of your domain name.
So already, a potential attacker will know you have a Drupal website and where to go to log into it.
Next, they'd need to know a username or email address for a user account on your website. How likely is it that one of these is "admin", "administrator", "editor", "webmaster" or something similarly generic? Another highly likely scenario is that your team members use their own name as their login and, almost certainly, their work email address.
It's not a huge task in this day and age for potential attackers to source a list of the names and email addresses of your team. Many of them are probably already published on your own website! More can be sourced via LinkedIn and other social platforms. Crawling Google for articles and documents featuring your organisation's name will also likely lead to more names and email addresses of your staff.
"There are more than 24 billion username and password combinations in circulation in cybercriminal marketplaces" (ii)
So a potential attacker knows where/how to log into your site and also has a list of possible usernames and email addresses that they can try in the first of the two fields protecting your site. They are therefore now only a password away from being able to gain access to your website. Only a password away from potentially being able to access your website user data, deface or take down your site, place exploits on the devices of your website visitors and more.
The big question is therefore: "how secure is that password?" - and what else can be done to further protect your website?
"While 65% of all respondents have some form of cybersecurity education...the reality is that 62% almost always or mostly use the same or variation of a password." (iii)
What can you do to increase your security?
Many of the tips for creating a strong, secure password have been shared hundreds of times previously - so much so that some almost feel clichéd now. They are, however, all still extremely relevant and more important than ever in a world of ever-increasing cyber attacks.
Password complexity
The first key step is to ensure that your password is suitably complex and secure - and this doesn't mean just starting it with a capital letter and adding a 1 and an exclamation mark to the end (see Michael McIntyre's words of wisdom on that topic!).
Equally though, it doesn't have to be a random group of characters that is so impossible to remember that you have to write it down or store it in a similarly insecure way to be able to remember it. Consider using a collection of random words or a sentence/phrase that means something to you that no one else would guess.
Use unique password
Avoid re-using the same password (or variations of it) across multiple platforms/services. You should particularly not use the same details for highly-sensitive work account as you do for your personal social media accounts or similar.
Use a Password Manager
Tools such as LastPass, Keeper or 1Password enable you to store your passwords in one place but then place additional layers of security on top to keep your data fully secure. You can therefore generate highly complex, unique passwords for each of your logins without having to worry about remembering them. You just save and recall them from the password manager instead.
Although there have been some high-profile concerns about the security of such tools in recent months (LastPass in particular), they still remain a much more secure method for managing passwords than many of the traditional alternatives. For example, many people allow their browser to store their passwords for them, but this is not always as secure as it may seem - particularly on portable devices such as laptops or mobiles. Here's one example of how easily passwords saved in your Google Chrome browser could be accessed and exploited.
Implement MFA
Above all else, the opening statement of this article is immediately voided by enabling Multi-Factor Authentication (MFA) on your accounts for as many services as possible. An increasing number of platforms now include an MFA option - some even insist on it, and rightly so.
By enabling MFA, you add an additional layer of verification to your logins, typically in the form of either a code being sent to you by SMS or email or via an authenticator app that you can install on your mobile/tablet. With this in place, even if your username/email address and password are exposed, attackers still won't be able to access your account without completing the additional MFA verification step.
Some people put off enabling MFA because it feels like it will add additional time and hassle to their logins, but the reality is that, once you start using it, it only typically adds a matter of seconds to the process. That's extra time very well spent to ensure your accounts remain secure. It's certainly more efficient - and vastly more secure - than having to search for your password in a notebook or on a post-it note!
Adaptive offer an MFA solution for Drupal websites which is already giving many of our clients additional security and peace of mind when it comes to their website accounts. We also offer a range of other cyber security services to further protect your Drupal website. Read more here or contact us for further details and free guidance.
Sources:
(i) LastPass/2019 Verizon Data Breach Investigations Report
(ii) Digital Shadows research, 2022
(iii) LastPass, "Psychology of Password findings" 2022

